As the Black Friday is passing by and people are buying items in bulk, on the same hand, Cyber Criminals are faking the iTunes invoice with the help of IRS to inject Malware into a Windows PC. The main aim of the Cyber Criminals is to steal a healthy amount of money from the person who is infected with the malware that they are trying to inject in the Windows PC. This Malware injection trick is said to be the oldest trick with amazing flaws and drawbacks from the Cyber Criminal’s side.
The main aim of this malware injection is to inject a Trojan on a PC running Windows by sending the user a fake iTunes invoice with the amount of $699.99. The amount which might not be way too surprising today because the Cyber Weekend is in full swing and you may think that you have spent on iTunes this much amount. The fact is that it is a Malware instead of the real iTunes invoice.

How Does the Malware is Injected in Windows?
The story of this fake iTunes invoice starts from an E-Mail that might be waiting your glance in your inbox with the name of iTunes invoice for a $699.99 Post Card that you bought today or sometime back in preceding months. After seeing the heavy amount of $699.99, first you will say WTF and then you will open the mail for sure to see about the fake iTunes invoice that you got from the Cyber Criminal. After you have opened the E-Mail, you will click on the links provided to you by that Cyber Criminal in the so-called iTunes invoice of $699.99 post card invoice. You can see the fake iTunes invoice pictured above by sophos.
As you can see the invoice looks similar to an Apple’s iTunes Invoice of a product purchase, but this iTunes Invoice is very different from the original one.
How to Identify Fake iTunes Invoice?
To identify this sort of fake iTunes invoice is not a hard task. As you can see the Billed to part of the invoice, it is not properly coded. It states (%Email%) that Means the E-Mail isn’t inserted in the invoice to whom the invoice has been mailed.
Then the view/download links in the invoice ends in download.jpg.exe that is an executable file and most probably the main file that is filled with Malware.
The two other options of “Cancel” and “Not Your Order” ends up in Check.php that seems to be affiliated with this .exe file to see if the Malware is infected or not in the PC by Cyber Criminal.
The story doesn’t ends here. When you click on other links, you will be redirected to a custom made page on which you will get an IRS warning that you are using a supported browser, even if you are using an updated version of the browser.
Once this page is displayed, it will download the exploit with the name of update.exe on your PC and it will execute the file to infect your computer with Zeus/ZBot Trojan.
How to Stay Safe from This Malware Attack?
To stay safe from this Malware is way easy than opening the Malware file and getting shocked to see the bill of $699.99 that was never spent by you.
All you need to do is just see for the sender of the E-Mail, install latest updates of your Anti-Virus, and don’t open E-Mails from the sender that you don’t know. Most of the time, E-Mails we get are infected in many different ways and we are not aware of the infection that is included in those E-Mails.
In order to stay safe from those E-Mails, all you need to do is see for the “TO” area of the E-Mail in which the recipient E-Mail is inserted “that is you.”
A quick heads up on this “TO” thing is as follows:
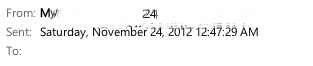
As you can see in the above image that the sender of the E-Mail is legit and the “TO” section is empty. The E-Mail was sent from Gmail to an unknown person, “that was me.” Therefore, this E-Mail was junk and might be full of Spam. However, the main point is that you must see the “TO” section always to distinguish between the Spam E-Mail and the real E-Mail. Even if the “TO” section points towards your E-Mail and you are not aware of the sender, then don’t open the E-Mail or download anything from the E-Mail. This will risk all your personal data.
Leave a Reply